Where Wizards Stay Up Late (19 page)

It was the Saturday before Labor Day and Thach noticed the streets were unusually quiet all the way through Westwood and onto the campus. Barker was already waiting on the loading dock at Boelter Hall with about a dozen other peopleâKleinrock, Crocker, Postel, Wingfield, Vint and Sigrid Cerf, and a handful of curiosity seekers. The Cerfs had brought along some champagne. Immediately upon seeing the crate, someone raised a question as to whether the crate would fit into the elevator; the IMP was unpacked so it could be wedged in.
When the machine was removed from the crate, the welcoming party was surprised by its size. Though smaller than the Sigma-7, it was not a small device. It was roughly the size of a refrigerator, weighing more than nine hundred pounds, and was formidably encased in battleship-gray steel, exactly to military specifications. There were four steel eyebolts on top of the IMP for lifting it onto a ship by crane or helicopter. At UCLA the IMP was like a soldier in combat fatigues crashing a faculty party.
When the elevator reached the third floor, the freight movers wheeled the machine down the hall and around the corner to its new home in room 3400. The Sigma-7 hummed nearby, oblivious to the massive disturbance that was about to invade its privacy. “It was a little like seeing your parents invite to dinner someone you've never met,” Crocker said. “You don't pay much attention until you discover they actually intend to marry you off to this stranger.”
Thach and Barker spent a few minutes cabling the IMP and powering it. Instantly the machine's core memory knew just what to do: It picked up just where it had left off in Cambridge, running the diagnostics that the IMP Guys had written for it. Next, Mike Wingfield attached his interface. Since this was node number one, there wasn't a network
per se
on which to test it. But Barker could do shunting experiments between the Sigma-7 and the IMP as they had done many times at Moulton Street between machines to simulate network links. Within an hour the Sigma-7 and the IMP were passing data back and forth as if they had been doing so for years.
Barker was still not absolutely certain that the synchronizer problem had been solved. But he was confident enough to consider going home. That night, Barker called Heart. “We're done, it's all working,” he said. “It's talking to Mike's [Wingfield] stuff. I'm thinking of getting a flight home in the morning.”
Heart paused, and Barker sensed what might be coming. “Why don't you just hang out there a few days?” Heart responded. “Just to see if something goes wrong.” Barker spent three days relaxing with Thach, touring Los Angeles, and waiting for the IMP to crash. It didn't.
A month after the first IMP was installed at UCLA, IMP Number Two arrived at SRI, right on schedule on October 1, 1969. That same month, Bob Taylor left ARPA. He had long since removed himself from the details of the network project. As he explained it, in the 1960s, “ARPA” was a magic word. Taylor's office was often called upon to sort out problems that others couldn't. In 1967 and 1968, Taylor had been sent repeatedly to Vietnam to help straighten out, among other things, the controversy over the Army's “body count” reports handled by the military information centers. The experience had left Taylor burned out. He took a post at the University of Utah.
Many milestones in the network experiment had been passed so far: Taylor's funding victory and successful wooing of Roberts; Roberts's network concept; BBN's construction and delivery of the first IMP. But the installation of IMP Number Two marked the most important achievement to date. At last the researchers could connect two disparate computers and get them talking to each other like a couple of old comrades.
Like the UCLA team earlier, SRI's group had a similar mad scramble getting ready for the arrival of the IMP. One crucial difference between the two sites was that whereas the UCLA guys disliked their Sigma-7, the SRI guys loved their host computer, an SDS 940. Like the Sigma-7, the 940 was built by Scientific Data Systems. But the Sigma-7 had been designed as a commercial processor, whereas the 940 was basically an academic device, a revolutionary time-sharing system first put together by a team of Berkeley researchers, later to be sold under the SDS nameplate. As a result, it was far more fun to program than the Sigma-7.
Bill Duvall, an SRI researcher, spent about a month writing a clever program for the 940 that essentially fooled it into thinking it was communicating not with another computer but with a “dumb” terminal. A dumb terminal can neither compute nor store information; it serves only to display the most recent set of information sent to it by the computer to which it's linked. Duvall's program was a very specific interim solution to the host-to-host communication problem. For weeks, the UCLA researchers had been preparing for their first log-in session by actually dialing into the SRI system long-distance using a modem and a teletype, to familiarize themselves with SRI's time-sharing system. With both IMPs now in place, and both hosts running, the moment to test the actual twoânode ARPA network had finally arrived.
The first thing to do, of course, was to connect. Unlike most systems today, which prompt the user for a log-in name and password, the SRI system waited for a command before acknowledging a connection. “L-O-G-I-N” was one of those commands.
Fastened to the first IMPs like a barnacle was a small phonelike box, with a cord and headset. It shared the line with the IMPs and used a subchannel intended for voice conversations. The voice line was, like the data line, a dedicated link. A few days after the IMP was in place at SRI, Charley Kline, then an undergraduate at UCLA, picked up the telephone headset in L.A. and pressed a button that rang a bell on the IMP in Menlo Park. A researcher in Engelbart's group at SRI answered it. It was somehow more thrilling to Kline than dialing a regular telephone.
The quality of the connection was not very good, and both men were sitting in noisy computer rooms, which didn't help. So Kline fairly yelled into the mouthpiece: “I'm going to type an
L
!” Kline typed an
L.
“Did you get the
L?
” he asked. “I got one-one-four,” the SRI researcher replied; he was reading off the encoded information in octal, a code using numbers expressed in base 8. When Kline did the conversion, he saw it was indeed an
L
that had been transmitted. He typed an
O.
“Did you get the
O?
” he asked.
“I got one-one-seven,” came the reply. It was an
O.
Kline typed a
G.
“The computer just crashed,” said the person at SRI. The failure came thanks to a clever bit of programming on Duvall's part. Once the SRI machine recognized the letters L-O-G, it completed the word. “I think that is where the bug was,” Kline recalled. “When the SRI 940 system received the
G,
it tried to send back “G-I-N,” and the terminal program wasn't ready to handle more than one character at a time.”
Later that day they tried again. This time it worked flawlessly. Crocker, Cerf, and Postel went to Kleinrock's office to tell him about it so he could come see for himself. Back in the UCLA lab Kline logged on to the SRI machine and was able to execute commands on the 940's time-sharing system. The SRI computer in Menlo Park responded as if the Sigma-7 in L.A. was a bona fide dumb terminal.
There is no small irony in the fact that the first program used over the network was one that made the distant computer masquerade as a terminal. All that work to get two computers talking to each other and they ended up in the very same master-slave situation the network was supposed to eliminate. Then again, technological advances often begin with attempts to do something familiar. Researchers build trust in new technology by demonstrating that we can use it to do things we understand. Once they've done that, the next steps begin to unfold, as people start to think even further ahead. As people assimilate change, the next generation of ideas is already evolving.
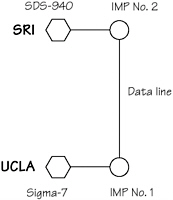
A network now existed. The first ARPA network map looked like this:
IMP Number Three was installed at UC Santa Barbara on November 1. For the Santa Barbara installation, Barker flew out to California again. By this time, Heart was more relaxed. There were few traces of the suspense that had attended the first trip. In fact, installing IMPs was beginning to seem routine.
Later that month, Larry Roberts decided to fly to California to inspect the network firsthand for the first time. Roberts didn't like to travel. When he did travel, he never left to catch his plane until the last minute. It drove his secretary crazy, but he missed only one plane that anyone could remember. That happened one afternoon when he was stopped for speeding on his way to Dulles Airport. Convinced that he hadn't been going too fast, Roberts decided to contest the ticket. He had been pulled over by the squad car near the point at which he had come onto the George Washington Parkway after a full stop, and his contention was that in that short distance he could not possibly have accelerated his Volkswagen Beetle to the speed alleged by the officer. Roberts went back to the scene and carefully measured off the distances. He gathered data on the engine output and weight of his VW bug, factored in Newton's law of inertia and made a few other calculations, and was prepared to go before a judge to make his case. It wasn't until friends convinced him he was unlikely to get a judge with a physics degree that he conceded the point and paid the fine instead of taking it to court.
Fortunately, there were no speeding tickets on this trip. Roberts and his program manager, Barry Wessler, flew to California without incident, and in Kleinrock's lab at Boelter Hall they watched the network in operation. This time, Kleinrock did the typing and in less than a minute he had logged on to the host computer at SRI. Roberts watched closely and left satisfied that the experiment was succeeding.
Fourth was Utah. By now it was Decemberâprime ski season. There also happened to be a Network Working Group meeting scheduled at the site. Keen skiers all, the whole BBN team, even Frank Heart, went to Salt Lake City to plug in the IMP. (Ironically, Barker was the only one excluded from the Utah tripâa fact he would not let the others forget for many years.)
The layout of the growing number of communications links was becoming an interesting problem. For one thing, there was not a point-to-point link between every pair of sites. For reasons of economy, Roberts decided that no direct link was needed between UCLA and Utah, or between Santa Barbara and Utah, so that all traffic destined for Utah had to go through the IMP at SRI. That was fine as long as it was up and running. If it crashed, the network would divide and Utah would be cut off until SRI was brought back on-line. As it would turn out, the four-node network that Roberts designed was not a robust web of redundant connections.
Disruptions in the system also manifested themselves in less obvious ways. This was made clear very early, when the students at Santa Barbara began doing exactly what Heart had feared they might: fiddling with their new toy. And their attitude was, Why not? They had never had to worry about outside connections, and it didn't occur to them that something they did in their computer lab might have an effect elsewhere. “We merrily thought the IMP was ours to play with,” recalled Roland Bryan, a Santa Barbara researcher. “We were testing it out, turning it on and off, resetting it, reloading it, and trying again.” As a result, people who were taking network measurements, and who counted on the network path through Santa Barbara, would have their experiment thrown off. “Although we did not hurt the links between other sites, we were disrupting the data traffic analysis being carried on by BBN and UCLA,” Bryan said. “We didn't think about the fact that every time we did that, someone out there would suffer.”
By the end of 1969, the Network Working Group still hadn't come up with a host-to-host protocol. Under duress to show something to ARPA at a meeting with Roberts in December, the group presented a patched-together protocolâTelnetâthat allowed for remote log-ins. Roberts was not pleased with the limited scope of the effort. Though Telnet was clearly useful and fundamental in that it let one terminal reach multiple remote computers, a remote login program by itself didn't solve the problem of letting two computers work together. Moreover, Telnet was a way to use the network, not a lower-level building block. Roberts sent them back to keep trying. After another year of meetings and several dozen RFCs, in the summer of 1970 the group reemerged with a preliminary version of a protocol for basic, unadorned host-to-host communications. When the “glitch-cleaning committee” finished its work a year later, the NWG at last produced a complete protocol. It was called the Network Control Protocol, or NCP.
